Campaign Overview
Microsoft says attackers are running a developer-targeting campaign that hides malicious code inside fake Next.js projects and supposed technical assessments. The goal is to trick developers, especially job seekers, into opening or running the projects as part of a normal workflow.
The campaign is dangerous because it blends into routine developer activity, such as:
- opening a repository in VS Code
- starting a local development server
- launching a backend service
In each case, the result is similar: attacker-controlled JavaScript is fetched at runtime and executed in memory, helping the attackers establish command-and-control (C2) access while leaving fewer traces on disk.
.png)
How Victims Are Lured
Threat actors create fake repositories on trusted developer platforms, including Bitbucket, and make them look like legitimate interview or assessment projects. One example Microsoft mentioned used a name like “Cryptan-Platform-MVP1.”
These lures are effective because they:
- appear to be normal coding assignments
- fit naturally into recruiting workflows
- target developers who are already accustomed to cloning repos and running unfamiliar code
Microsoft said this activity fits a broader pattern of job-themed social engineering aimed at increasing the chance that victims will execute malicious code voluntarily.
Three Main Execution Methods
Microsoft identified three different execution paths, all leading to the same malicious JavaScript payload:
- VS Code workspace execution: The malicious project includes a VS Code workspace task configured with runOn: "folderOpen". When the developer opens and trusts the folder, the task automatically runs and retrieves malicious code from a Vercel-hosted domain.
- Build-time execution during development: Simply running npm run dev c an activate the malware. In this method, attackers hide malicious logic inside altered JavaScript files pretending to be normal libraries such as jquery.min.js. That code then downloads another loader and executes it in memory through Node.js.
- Server startup execution: Starting the backend triggers hidden loader logic placed in a backend module or route file. This loader can exfiltrate environment variables to an external server and then execute JavaScript received in response, again directly in memory. All three methods are designed to look like ordinary developer actions while secretly enabling remote access.
What the Malware Does
After execution, the payload begins by profiling the compromised machine and contacting a registration endpoint to obtain a unique instance ID. That ID is then used in later communication so the attackers can track and manage the infected host.
A second-stage controller can then:
- receive and run more JavaScript in memory
- maintain persistence and session continuity
- send error reports back to the attackers
- retry failed operations for resilience
- track spawned processes
- stop activity cleanly when instructed
- support further discovery and data exfiltration
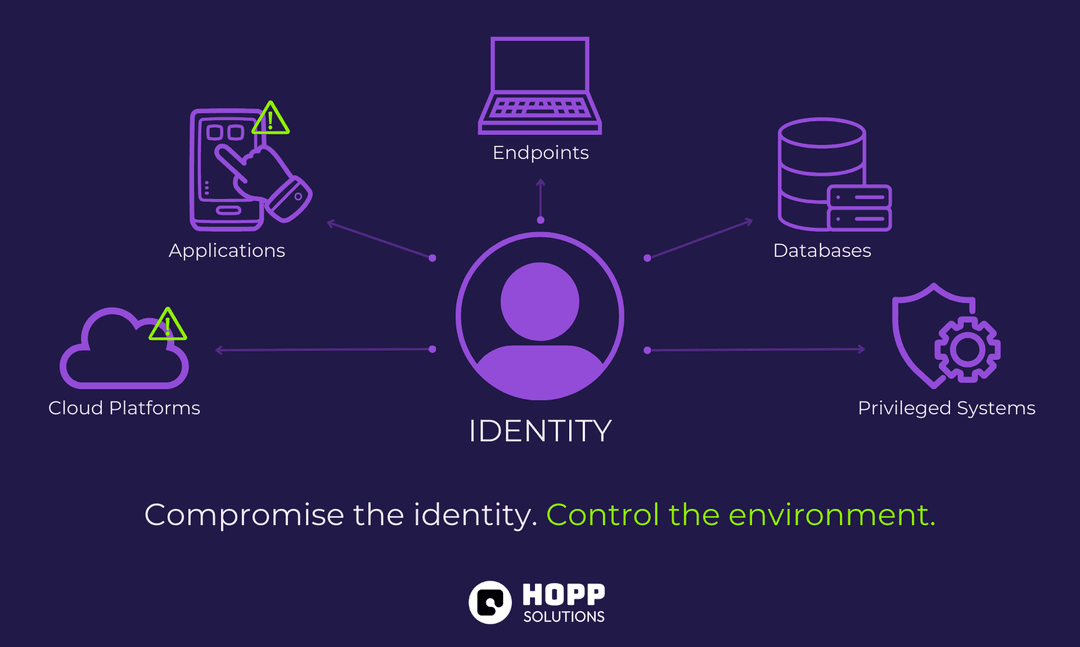
This makes the campaign more than a one-time infection attempt. It is built to give operators stable, persistent access to developer systems, which often contain valuable assets such as:
- source code
- secrets and tokens
- credentials
- access to internal networks and build systems
Related Findings from Other Security Companies
Microsoft did not officially attribute the campaign, but the methods strongly resemble North Korea-linked “Contagious Interview” activity, which has long used fake job opportunities to target developers.
Other researchers found the campaign is evolving:
- Abstract Security saw attackers move beyond Vercel and begin using GitHub Gists and URL shorteners like short[.]gy to hide malicious staging infrastructure. • The same researchers identified a malicious npm package called eslint-validator, which downloads an obfuscated payload from Google Drive. That payload is associated with BeaverTail, a known JavaScript malware family.
- Another GitHub-hosted attack chain used a malicious VS Code task on Windows to download Node.js if needed, decode hidden content, and deploy PyArmor protected Python malware.
- Red Asgard reported that some samples retrieved JavaScript through the Polygon blockchain, specifically from data stored in an NFT contract, making the payload delivery chain harder to disrupt.
- The final malware in some cases acts as an information stealer, targeting browser data, wallet contents, and password manager information.
Broader Impact and Recommended Defenses
Microsoft said organizations should respond by strengthening developer workflow trust boundaries and reducing the risks of running untrusted code. Recommended defenses include:
- Enforcing strong authentication and conditional access
- Maintaining strict credential hygiene
- Applying least privilege to developer accounts and build identities • isolating build infrastructure where possible
The broader scale of the threat is significant:
- GitLab said it banned 131 accounts in 2025 linked to malicious code distribution tied to Contagious Interview and the Wagemole fraudulent IT worker scheme.
- In over 80% of cases, the attackers used at least six legitimate services to host malware, including Vercel, Render, Railway.app, JSON Keeper, Mocki, and npoint.io.
- GitLab also uncovered a private project likely tied to a North Korean IT worker cell, with records showing over $1.64 million in earnings from Q1 2022 to Q3 2025.
- Okta added that while many fake IT worker attempts fail early, some actors are improving, becoming more convincing, and scheduling hundreds of interviews.
Overall, the campaign shows how a seemingly ordinary interview project can become a fast path to remote code execution, persistence, and data theft when attackers exploit normal developer habits.
.png)